
How Open Source Tools Are Shaping the Future of Cybersecurity
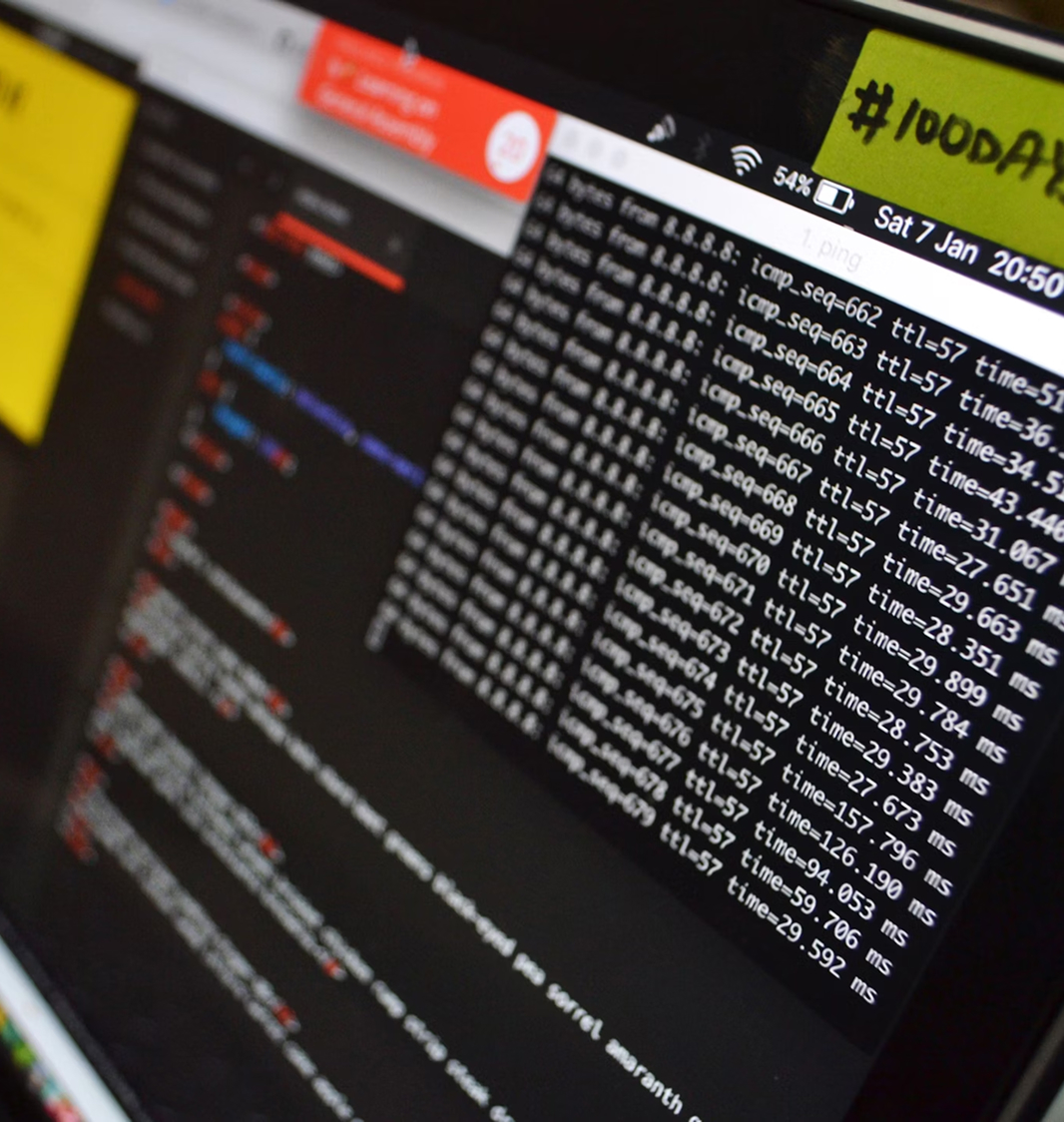
Dive into how open-source solutions are accelerating threat detection and democratizing cybersecurity innovation.

Director of Threat Research, SentinelOps
Our cybersecurity conference directory is meticulously updated and checked manually to prevent spam, ensuring it remains the community’s premier resource for discovering top cybersecurity conferences, events, meetings, and seminars for 2024, 2025, and beyond. This carefully curated list caters to chief information security officers (CISOs), cybersecurity leaders, technology executives, and anyone passionate about the field.
Discover today’s top cybersecurity conferences, seminars, and industry events happening globally. Stay updated with the latest infosec trends, expert speakers, and networking opportunities—all in one place.
AWS re:Invent 2025 is one of the most influential gatherings in the global cloud and cybersecurity ecosystem. Held annually in Las Vegas, this event draws tens of thousands of professionals to explore the forefront of innovation in cloud infrastructure, data security, and enterprise computing. As cloud adoption intersects more deeply with security, re:Invent continues to showcase how AWS services enable resilient, secure, and scalable environments for organizations of all sizes. The event includes keynotes from top executives, including AWS CEO Matt Garman, who introduce groundbreaking services and future-facing cloud strategies.
Attendees benefit from in-depth technical sessions, hands-on labs, and exclusive announcements tailored to developers, engineers, and security professionals alike. Networking opportunities span across peer-to-peer meetups, workshops, and expert panels, offering real-world insights from the builders behind AWS. The conference serves as both an educational deep dive and a strategic vision summit, positioning attendees at the center of cloud innovation. For cybersecurity stakeholders, re:Invent provides essential visibility into emerging security tools and infrastructure best practices shaping the digital enterprise.
Physical • Paid • Part of Amazon Web Services (Aws)
The IT Security Summit, held from December 1-4, 2025, in Munich or online, offers cybersecurity professionals a hands-on experience to master real-world challenges. The conference emphasizes actionable strategies in DevSecOps, Zero Trust, and secure software development, focusing on securing APIs, protecting cloud infrastructure, and integrating AI-driven defenses. It is designed for those seeking to proactively address today's toughest IT threats.
Hybrid (Both) • Paid • Part of Software & Support Media Gmbh
PasswordsCon (Passwords Conference) is the first conference in the world focusing on passwords, PINs, and anything related to digital authentication. The conference was started in December 2010 at the University of Bergen, Norway.
PasswordsCon has previously been held at the universities in Bergen, Oslo, and Trondheim (Norway), the University of Cambridge (UK) and at the Ruhr University Bochum (Germany).
PasswordsCon has also been held as a separate track at the Swedish Internet Days in Stockholm, as a stand-alone conference in Las Vegas and as a separate track at the BSides Las Vegas conference.
Hybrid (Both) • Paid • Part of Passwordscon
Dive into the world of cybersecurity excellence with an immersive training experience at SANS Dallas 2025 (December 1-6, CT). Led by world-renowned instructors boasting extensive industry experience, this training event offers live access to top experts in the field.
SANS Dallas 2025 is equipped with industry-leading hands-on labs, simulations, and exercises that you can immediately apply upon your return to work.
Hybrid (Both) • Paid • Part of Sans Institute
Sweden, a global leader in digital innovation, faces an increasing number of cybersecurity threats targeting its critical infrastructure, financial institutions, healthcare systems, and government entities. The Heliview State of Cybersecurity December 2025 will take place on December 2, 2025, at Bygget Konferens, bringing together cybersecurity professionals, industry leaders, and policymakers to tackle these pressing challenges.
As cyber-attacks on Swedish organizations intensify—whether from foreign adversaries, financially motivated cybercriminals, or independent threat actors—the need for robust cybersecurity strategies, risk mitigation frameworks, and enhanced national defenses has never been greater. This conference will provide insights into the latest cyber threats, regulatory developments, and innovative defense mechanisms to safeguard digital infrastructures.
Attendees will have the opportunity to exchange knowledge, explore cutting-edge cybersecurity solutions, and expand their professional networks. Whether you are a CISO, IT security leader, or risk management professional, this event is essential for staying ahead of cyber threats and ensuring the resilience of Sweden’s digital landscape. Join us in Stockholm and be part of the solution to securing Sweden’s digital future.
Physical • Paid • Part of Heliview Conferences & Training
The CyberRisk Leadership Exchange in Boston is designed for CISOs, security executives, and senior practitioners looking to stay ahead of the most pressing cyber threats. This event fosters collaborative discussions around risk management, compliance, and emerging technologies that are transforming enterprise security.
Attendees will engage in curated sessions that emphasize practical strategies for building cyber resilience, addressing regulatory pressures, and navigating the complex digital risk landscape. With expert insights and peer exchange, this event helps leaders sharpen their strategies to safeguard critical infrastructure and data.
Physical • Free • Part of Cyberrisk Alliance
One of the most important Polish conferences on cybersecurity is back! Oh My Hack is a meeting of cybersecurity experts and enthusiasts who share best practices in the field of cybersecurity.The 7th edition of the OMH conference will take place on 2 December 2025 at PGE Narodowy in Warsaw.
Meet leading cybersecurity experts and exchange experiences. Select the most interesting among dozens of inspiring presentations and see them live. Learn about the latest case studies and solutions in IT security. Make valuable contacts with company representatives and develop a career in cybersecurity. Gain access to recordings of all lectures (within 6 tracks) after the event.
Adam Haertle, founder and editor-in-chief of the website Zaufana Trzecia Strona and co-host of the podcast Rozmowa Kontrolowana, is responsible for the high content value of the conference. The event is produced in collaboration with the PROIDEA team
Physical • Paid • Part of Proidea
AISS, an industry-led conference, is characterized by presence of a diverse set of stakeholders, themes, sub themes, topics and sub-topics, multiple tracks, varied session formats and plethora of activities and experiences that make up for a rich three-day engagement and learning for the delegates. This edition shall entail deliberations organized around the broad areas of Security Technology Leadership, Security & Privacy Governance, Data, Digitization & Data Sharing, Future of Cyber Crimes, Response & Resiliency, Intersection of AI & Quantum, strategic capacity building, geopolitics & cyber diplomacy et. Al.
The core and fundamental intent of the Summit would be to enable, facilitate, organize, and orchestrate collective learning, experience sharing, impactful dialogues, differential diagnoses of the topical Security & privacy issues and challenges, consensus building and future casting. This enablement would happen by capitalizing on the elements such as perennial ideas, contextual awareness, technological capabilities, problems and use cases. From supporting the country's ambitious digital transformation initiatives to addressing the evolving threat landscape, the event has endeavoured to chart the future roadmap in the realm of Cyber Security.
An eclectic line up of speakers and subject matter experts from across the board and different parts of the world shall come together to share their perspective as part of different sessions and formats. AISS 2025 shall host sectoral meetups, sub summits, parallel track sessions, fire side chats, short presentations, Masterclasses, and host of other formats. The Summit shall also be hosting the thirteenth edition of the Excellence Awards which have been celebrating the noteworthy contributions of individuals and organizations to the subject and profession of Cyber Security & Data Protection.
Physical • Paid • Part of Data Security Council Of India
AVAR 2025 is the 28th edition of AVAR’s international cyber security conferences. AVAR’s conferences have been held every year since 1998 and are a pivotal forum for the cyber security community, gathering practitioners, thought leaders, and agenda setters to network, share knowledge, and identify avenues for cooperation that can enhance global cyber security. AVAR 2025 recognizes the growing importance of interaction between cyber security practitioners and management and includes awards for CISOs along with CISO oriented knowledge sessions and panel discussions to create networking opportunities between the researchers’ community and corporate leaders.
Physical • Paid • Part of Avar (Association Of Anti Virus Asia Researchers)
The IDC CIO Summits serve as premier gatherings for technology leaders to explore the dynamic role of Chief Information Officers (CIOs) in steering innovation, leadership, and digital transformation. In today’s fast-paced digital landscape, CIOs have transitioned from being traditional IT managers to influential strategists and business leaders. This event delves into the strategies and insights needed to thrive in this evolving role.
As technology becomes the cornerstone of business innovation, CIOs are now pivotal in shaping organizational success. The summit offers a platform to learn from industry experts, share experiences, and gain actionable insights into balancing cutting-edge technologies with practical applications. Attendees will discover how to position themselves as strategic leaders, drive business transformation, and navigate the challenges of rapid technological change.
Today’s CIOs are not just adapting to change—they are at the forefront of it. They collaborate with executive teams, implement forward-thinking strategies, and ensure technology aligns seamlessly with business objectives. The IDC CIO Summits provide an invaluable opportunity to deepen your understanding of this critical role and leave equipped with tools to enhance your digital journey. Don't miss the chance to redefine your leadership approach and propel your organization into the future.
Physical • Paid • Part of Idc
Operation: Defend The North 2025 delivers a high-impact experience designed to test and sharpen Canada’s response to a large-scale cyber attack. Set against the backdrop of escalating digital threats, this event immerses participants in a fast-paced tabletop scenario that simulates coordinated attacks on sectors such as energy, finance, healthcare, government, and telecommunications. By placing professionals in the center of crisis decision-making, it challenges their ability to collaborate, respond, and recover under pressure.
Designed for both online and in-person attendees, this exercise offers a rare opportunity to bridge gaps between private and public sectors. Industry experts, security specialists, and policymakers come together to share insights, evaluate existing response frameworks, and explore improvements in national cyber defense. Whether you're a seasoned CISO or a government official, this event provides a powerful, hands-on environment to stress-test strategies and strengthen resilience across Canada’s digital frontlines.
Hybrid (Both) • Paid • Part of Siberx
Don’t miss the Atlanta Cybersecurity Conference! Get key insights into cybersecurity trends for 2025, connect with industry experts, and participate in hands-on discussions with global providers. Reserve your place to stay ahead of emerging threats and strengthen your organization’s defenses.
The $150 admission (without a promo code) covers catered meals, a networking cocktail reception, and full access to presentations, keynotes, panels, and the exhibit hall.
Focused solely on cybersecurity solutions and threats, this event targets professionals responsible for security purchases. Sponsors and exhibitors are sales engineers and marketing experts, not recruiters.
For career growth, visit CyberNexus.World's membership portal and job board.
Physical • Paid • Part of Data Connectors
The CyberRisk CISO Dinner in Los Angeles offers a unique space for cybersecurity leaders to connect and exchange perspectives on today’s evolving threat landscape. Attendees explore solutions for securing data, mitigating risks, and driving organizational resilience.
This private dinner creates a collaborative atmosphere that strengthens professional connections among CISOs and provides tangible strategies for advancing enterprise security programs.
Physical • Free • Part of Cyberrisk Alliance
The CyberRisk CISO Dinner in Phoenix creates a trusted forum for chief information security officers and senior cyber leaders to exchange insights. With a focus on local challenges and global cyber trends, the dinner encourages discussion on pressing issues such as cloud security, ransomware defense, and regulatory compliance.
The format emphasizes meaningful networking and practical takeaways. Attendees benefit from peer collaboration in a relaxed setting that fosters open sharing of strategies and solutions.
Physical • Free • Part of Cyberrisk Alliance
ERTL-YANG Leader Summits bring together C-level executives, technology leaders, and decision-makers to discuss emerging trends, leadership strategies, and the evolving role of technology in business transformation. These exclusive summits provide a platform for networking, collaboration, and thought leadership, covering key topics such as digital innovation, cybersecurity, AI integration, cloud transformation, and risk management.
With a strong focus on executive insights and peer-to-peer discussions, ERTL-YANG Leader Summits offer a unique opportunity for leaders to exchange ideas, share best practices, and shape the future of enterprise technology.
Physical • Paid • Part of Ertl-Yang
SecureWorld is a leading cybersecurity conference offering a blend of in-person and online events for InfoSec professionals. It features keynote speakers, panels, and workshops, providing opportunities to earn CPE credits. Attendees can network, explore solutions, and engage with security associations, enhancing both technical skills and strategic approaches. SecureWorld fosters collaboration and professional growth, attracting thousands seeking insights and a robust professional network.
Online • Paid • Part of Secureworld
FutureCon Events offers dynamic cybersecurity conferences featuring high-level training on security strategies and risk management. Attendees join leading professionals and C-level executives who share real-world experiences in mitigating cyber risks. These events empower C-suite leaders and CISOs with knowledge to combat cybercrime and build resilient organizations. Participants gain insights on application security, explore cutting-edge technologies, and discuss pressing issues, while networking with peers and global cybersecurity leaders.
Physical • Paid • Part of Futurecon Cybersecurity Events
Defending The Enterprise
Join us for the 3rd edition of CISO Edge Espana and discover how CISOs and IT Security leaders from Spain’s most influential business organizations come together to discuss delivering their Enterprise Cybersecurity strategy.
This is an exclusive opportunity for leaders to hear from experts, tap into the collective intelligence of the region’s top thought leaders, and learn the next steps from their peers on similar journeys, leveraging the enabling value of technology
On the 4th of December, 2025, in Madrid, we will showcase keynote presentations, roundtables, and panel discussions led by the most innovative CISOs and IT Security leaders driving business and technology initiatives for Spain’s most successful national and global brands
Physical • Free • Part of Ciso Edge Emea
Conf42 is a series of global technology conferences that focus on bringing together professionals, enthusiasts, and experts in the fields of software development, cybersecurity, artificial intelligence, DevOps, and more. These conferences are meticulously curated to provide valuable insights into the latest trends, technologies, and challenges within the tech industry. With a wide array of topics covered, Conf42 caters to a diverse audience ranging from seasoned developers to budding technologists.
Each conference includes engaging keynotes, technical deep dives, and panel discussions led by industry leaders. Attendees gain access to cutting-edge knowledge on emerging tools and best practices, as well as actionable strategies to improve their work. Networking opportunities abound, allowing participants to connect with peers, share ideas, and collaborate on innovative projects. By fostering a vibrant community of tech enthusiasts, Conf42 continues to inspire innovation and professional growth in the ever-evolving technology landscape.
Whether you're exploring advancements in cybersecurity or delving into machine learning, Conf42 serves as an invaluable resource for staying ahead in the fast-paced world of technology.
Online • Free • Part of Conf42
CIO NetworX London offers an exclusive evening for senior IT leaders to engage in high-level discussions and targeted networking. With only 24 seats available, the event provides a structured yet fluid programme that maximizes strategic connections through pre-arranged meetings and dynamic roundtable sessions. The evening includes a private insight dinner, ensuring attendees can delve deeper into emerging IT challenges and explore innovative solutions. This gathering fosters peer-to-peer engagement, enabling meaningful collaborations to drive enterprise transformation.
Physical • Paid • Part of Global Cxo Institute
The 3rd Annual Jacksonville Cybersecurity Summit connects cybersecurity executives and seasoned practitioners responsible for protecting their companies’ critical infrastructures with innovative solution providers and renowned information security experts. Admission offers attendees access to all interactive panels, discussions, catered breakfast, lunch and cocktail reception.
Physical • Paid • Part of The Official Cyber Security Summit
The CyberRisk CISO Dinner in Washington DC provides an intimate and highly focused environment for security leaders to connect and share knowledge. This private-format gathering enables candid dialogue about the challenges of managing risk, compliance, and evolving threat landscapes in both the public and private sectors.
By bringing together top CISOs in the region, this dinner promotes peer-to-peer networking and real-world problem-solving. Attendees leave with actionable ideas and strengthened connections that support their leadership roles in cybersecurity.
Physical • Free • Part of Cyberrisk Alliance
Just like the other chapters of BSides around the world, BSides Cape Town is an annual Information / Security conference that is different. We are a volunteer organised event, put on by and for the community. Each year there is a staff of committee members and volunteers.
There is a nominal fee charged to the public to attend BSides Cape Town. Currently, almost 100% of our costs are covered by our generous donors and sponsors, who share our vision of sharing information. The conversations we start are always relevant to what’s happening right now and in many instances include practical demos instead of the old school lecture style cons. The Cape Town chapter of BSides can be dated back pre 2012. You can read more about that here. To get involved, keep an eye out on Meet-up and @0xc0ffee_cpt on twitter, and join our community of like minded hackers on the second Saturday of each month.
Physical • Paid • Part of Bsides Cape Town Npc
CyberMarketingCon 2025 is a conference designed specifically for professionals focused on marketing within the cybersecurity industry. The event addresses the unique challenges faced by marketers in this highly technical and fast-changing field, offering strategies and insights directly from experienced peers working at cybersecurity companies. With sessions tailored to the realities of this specialized space, the event ensures attendees leave with actionable ideas they can apply to their businesses.
The program combines workshops, keynotes, and hands-on discussions to give marketers both inspiration and practical tools for improving campaigns, strengthening messaging, and demonstrating ROI. Beyond the sessions, the conference is also a powerful networking hub, allowing attendees to build lasting relationships in a small but growing professional community. Expert consults and real-world case studies round out the experience, making CyberMarketingCon 2025 a must-attend event for those who want to stay competitive in cybersecurity marketing.
Physical • Paid • Part of Cybersecurity Marketing Society
The Gartner Identity & Access Management (IAM) Summit 2025 is a premier event for cybersecurity professionals, IT leaders, and business decision-makers focused on safeguarding digital identities and ensuring secure access in an increasingly interconnected world. This annual summit offers cutting-edge insights, strategies, and solutions to address the evolving challenges of identity and access management.
Participants will explore topics such as zero-trust security, identity governance, risk management, and advanced authentication technologies. With expert-led sessions, real-world case studies, and interactive workshops, the event provides actionable advice to help organizations enhance their cybersecurity posture and meet compliance requirements. The summit also highlights the latest IAM tools and innovations, empowering businesses to streamline processes, reduce risks, and improve user experiences.
Join industry leaders, Gartner analysts, and technology providers at this must-attend event to stay ahead of emerging threats, collaborate with peers, and gain the knowledge needed to shape your organization’s IAM strategy for 2025 and beyond.
Physical • Paid • Part of Gartner
The Open Source Summit Japan 2025 is set to be a premier gathering for developers, technology leaders, and open-source enthusiasts in Japan. Taking place in the heart of Japan's tech landscape, the summit will focus on the latest trends, innovations, and developments in the open-source community. Attendees will have the chance to connect with industry professionals, share knowledge, and explore emerging technologies that are shaping the future of software development. As open-source projects continue to drive the digital transformation of industries, the event will offer valuable insights for those eager to contribute to and learn from global initiatives.
Throughout the summit, participants will experience a variety of sessions, including technical talks, panel discussions, and hands-on workshops. These sessions will cover a range of topics from cloud computing and security to DevOps and automation. Whether you are a beginner or an experienced developer, Open Source Summit Japan 2025 offers something for everyone. With expert speakers from leading companies and open-source foundations, this event will be an excellent opportunity for networking, professional growth, and gaining the latest knowledge to stay ahead in the rapidly evolving tech landscape.
Physical • Paid • Part of Linux Foundation
Die NIS-2-Richtlinie stellt Unternehmen vor neue Herausforderungen: Regelmäßige Risikoanalysen, technische und organisatorische Maßnahmen sowie Schwachstellenmanagement sind verpflichtend geworden. Doch was bedeutet das konkret für die Praxis?
In unserem 2-tägigen IT Security Camp mit Christian Schneider erhalten Sie nicht nur tiefgehendes Wissen über Angriffstechniken & Sicherheitsmaßnahmen, sondern auch die praktischen Fähigkeiten, um IT-Risiken zu identifizieren und geeignete Gegenmaßnahmen zu implementieren - exakt das, was NIS-2 fordert.
Das Camp vermittelt praxisnahe Attack & Defense-Techniken, die für eine sichere Softwareentwicklung und den Schutz Ihrer IT-Infrastruktur essenziell sind.
Online • Paid • Part of Software & Support Media Gmbh
A successful project starts with a well-founded estimate of the costs. The 4-day Cost Estimating Foundation training will teach you the basics of cost estimation. You will learn approaches for different aspects of the estimating profession and how to apply them in your daily work.
During this training, we emphasize practical experience as well as theoretical knowledge. Several small cases will be prepared during the training. This helps you familiarize yourself with the knowledge you have just gained and apply it to real-world situations. At the end of the Cost Estimating Foundation training you will have:
An understanding of cost estimation, cost control, and planning definitions. You will also be able to read cost engineering reports and put it in the perspective of your project
The knowledge to prepare and evaluate estimates quicker and more accurately. This will immediately affect the control you have over the cost of your project
The ability to make your factor estimates and validate factor estimates prepared by others
The knowledge to identify major cost risks of engineering. Together with the estimating methods, this means you will be able to estimate the engineering involved in your projects
Hybrid (Both) • Paid • Part of Imf Academy
IT-Tage 2025 – A Conference for Software architecture, Software development, DevOps, AI, Cloud, database, IT-Security, Agile and IT-Management.
Deepen your knowledge and enjoy the opportunity to get to know new people from the industry. With 16 sub-conferences, over 220 sessions, workshops and keynotes you will have 4 day full of interesting topics, meetings with experts and entertainment. Other topics that will be featured this year: Digital sovereignty, Open Source, IT & Society and New Work. We want to know how we can shape our future by creating visions and finding possible solutions.
For more Information visit www.it-tage.org
Physical • Paid • Part of Alkmene Verlag Gmbh
The AI_dev: Open Source GenAI & ML Summit 2025 is a premier event bringing together leading experts, developers, and researchers in the fields of Artificial Intelligence (AI), Machine Learning (ML), and open-source technologies. This highly anticipated summit offers a platform for sharing knowledge and exploring cutting-edge advancements in generative AI and machine learning. Attendees will gain insights into the latest trends, best practices, and open-source tools that are shaping the future of AI technology.
Throughout the summit, thought leaders and innovators will discuss key topics ranging from the ethical implications of AI to the evolving landscape of machine learning frameworks and algorithms. Attendees can expect in-depth sessions, interactive workshops, and networking opportunities with like-minded professionals. The event also provides a unique space for collaboration, where developers and researchers can connect and explore the latest open-source contributions to GenAI and ML. With an emphasis on community-driven progress, AI_dev 2025 is the go-to event for anyone looking to stay ahead in the fast-moving world of AI and open-source development.
Physical • Paid • Part of Linux Foundation
Discover today’s top cybersecurity conferences, seminars, and industry events happening globally. Stay updated with the latest infosec trends, expert speakers, and networking opportunities—all in one place.
Explore expert-written articles on the latest trends in cybersecurity, threat intelligence, data protection strategies, and industry insights. Stay informed with curated content from top infosec professionals, analysts, and thought leaders.

Dive into how open-source solutions are accelerating threat detection and democratizing cybersecurity innovation.

Director of Threat Research, SentinelOps

A breakdown of the newest ransomware tactics, techniques, and procedures (TTPs), and how organizations can build more resilient defenses.

Security Analyst, CyberEdge Labs

Learn the key components, challenges, and implementation best practices for adopting Zero Trust security frameworks in modern organizations.

Cloud Security Consultant, NetSecure Solutions